Update: if you enjoy this post, we did a follow-up livestream (based on a very popular presentation I gave at MeasureCamp), now available on youtube, that walks through specific examples of how cookies work (I promise, you may be surprised) and the misleading narratives we tell about consent and server-side tag management.
(This is cross-posted from the 33 Sticks blog.)
I know we’re all sick of hearing about the “cookieless future”. As a topic, it somehow manages to be simultaneously boring (it gets too much air time) and terrifying (the marTech world is ending). But I want to discuss the problematic word itself, “cookieless”. I get that a lot of people use it metaphorically- they know that cookies as a general concept are not going anywhere; we just need a way to refer to all the changes in the industry. But I still argue the phrase is ambiguous at best, and misleading at worst. If someone brings up “the cookieless future” they might be talking about:
Technology Limitations
- Browsers and ad blockers blocking 3rd party cookies (like Chrome will maybe-probably-someday do, and which Safari and other browsers have already been doing for years)
- Browsers blocking or capping certain 1st party cookies (like Safari’s ITP)
- Browsers and ad blockers blocking tracking technology (like Safari’s “Advanced Tracking Protection”, which blocks not just analytics, but GTM altogether)
- Browsers and ad blockers blocking marTech query params like gclid or fbclid
- App ecosystems blocking the use of device identifiers within apps (like Apple’s ATT)
OR Privacy and Consent
Depending on your jurisdiction:
- Your users may have the right to access, modify, erase or restrict data you have on them. This applies to data collected online tied to an identifier, as well as PII data voluntarily given and stored in a CRM.
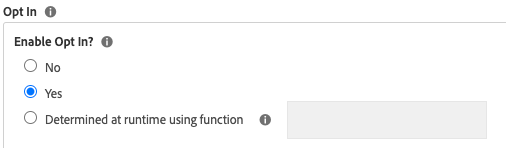
- Your users have the right to not be tracked until they’ve granted permission (GDPR), or to opt-out of their data being shared or sold (CCPA and many others)
- Data must be processed and stored under very specific guidelines
You’ll note under the “Privacy and Consent” list, I don’t mention cookies. That’s because laws like CCPA and GDPR don’t actually focus on cookies. CCPA doesn’t even mention cookies. GDPR is very focused on Personal Information (which is broader than Personally-Identifiable Information, or PII. Personal Information refers to anonymous identifiers like you might find in marTech cookies, but it also refers to IP addresses, location data, hashed email addresses, and so on). Again, for those in the back: CONSENT IS FOR ALL DATA THAT HAS TO DO WITH AN INDIVIDUAL, NOT JUST COOKIES. Cookies are, of course, a common way that data is tied to a user, but it is only a portion of the privacy equation.
I understand why we want one term to encapsulate all these changes in the industry. And in some ways, it makes sense to bundle it all together, because no matter the issue, there is one way forward: make the best of the data we do still have, and supplement with first-party data as much as possible. However, this conflation of technology (chromeCookiePocalypse) with consent (GDPR) has led to exchanges like this one I saw on #measure slack this week:
Q: “After we implemented consent, we noticed a significant drop in conversions. How can we ensure accurate tracking and maintain conversion rates while respecting user privacy?”
A: “Well, that’s expected, isn’t it? You will only have data from those who want to be tracked. If folks opt out, you will have less data.”
Q: “Yes, we expected a dip in conversion, however our affiliates are reporting missed orders and therefore commission discrepancies, which is affecting our ranking. They suggested API tracking and also said that since they are using first party cookies, they should not be blocked, and we should categorize them as functional“.
Sigh. People are understandably confused. First-party cookies don’t need consent, right? Privacy just means cookie banners, right? Losing third-party cookies will mean a lot of lost tracking on my site, right? If we solve the cookie problem, work can continue as normal, right? (Answers: no, no, no, and no).
Even people who should know better are confused. The focus on cookies has silliness like this happening:
- Google’s “cookieless” pings that collect data even if a user has requested to not have their data collected
- Sites removing ALL cookies from their site (talk about throwing the baby out with the bathwater, if baby-throwing took a lot of effort and resources)
- Server-side tag management being touted as “vital for a cookieless future” (as if adding a stopping point between the user’s browser and data collection points somehow reduces the need for lasting identifiers in the user’s browser, or for consent. Server-side tag management has advantages, but it just shifts the cookie and consent issues. It doesn’t solve them. )
- People thinking that a Javascript-based Facebook’s CAPI deployment will provide notable, sustained protection against online data loss (I have a whole other blog post about this I need to finish up)
- Technology vendors pivoting from using anonymous online identifiers in cookies tied to one browser instance, to using online identifiers tied to personal emails and phone numbers. (One might argue this does not feel like a step forward.)
- Agencies selling “third-party cookie audits”, to scan your site for third party cookies and help you document and quantify each one to prepare for the impending loss of data.
I want to talk specifically about this last one. This idea (that auditing your site for cookies is a key way to prevent data loss due to Chrome blocking 3rd party cookies) has been a key talking point at conferences, has been promoted by agencies and vendors selling their 3rd-party-cookie-auditing services, and is even promoted by Google’s don’t-panic-about-us-destroying-the-ad-industry documentation.
But all the ChromeCookiePocalypse dialog- and the cookie audit recommendations- leaves out critically important context (especially if we’re talking to an audience of analysts and marketers):
- Between Safari, Firefox, Opera, and Brave (not to mention ad blockers), 3rd party cookies have not been reliable for some time. There is a good chance more than 50% of your traffic already blocks them, and the world continues to turn, partially because of so much mitigation that’s already been done: Adobe Analytics, Google Analytics, Facebook, Adwords, Doubleclick, etc… all already use 1st party cookies for tracking on your site (that “on your site” bit is important, as we’ll discuss in point #4).
- That said, we can’t pretend that if we fix/ignore the 3rd party cookie problem, then our data is safe and we can continue business as usual. Yes, 3rd party cookies are being blocked, but even 1st party cookies may be capped or limited because of things like Apple’s ITP. Some browsers and/or ad blockers may block tracking even if it’s first-party. And there are other issues: bots are rampant on the web and most tools do a poor job of filtering them out. Browsers strip out query parameters used to tie user journeys together. Depending on your local privacy laws, you could be losing a significant portion of your web data due to lack of consent (I’ve seen opt-out rates up to 65%). All data collected online is already suspect.
I suppose it’s better late than never, but even if Chrome weren’t changing anything, you should already be relying on first-party data wherever possible, supplementing with offline data as much as possible. - A thorough audit of 3rd party cookies is not going to tell you what you need to know. I, as a manager-of-tags tasked with such an audit, can tell you your site has a Doubleclick cookie on it. I can’t tell you what strategies go into your Doubleclick ads. I can’t tell you how much of your budget is used on it. I can’t even tell you if anyone is still using that tracking. I can’t tell you from looking at your cookies how your analysts use attribution windows, or if you currently base decisions off of offsite behavior like view-through conversions. I can’t tell you, based on your cookies, if you have a CDP that is integrated with your user activation points.
Even if the cookies alone were the key factor, a scan or a spot-check of your own site is likely to miss some of the more important cookies. If I come directly from Facebook or Google to a site, then I may have cookies that wouldn’t be there if I came directly to the site. If I’ve ever logged in to Facebook or Google within my browser, that will add even more 3rd party cookies on my site. It would be virtually impossible to audit all of those situations to find all of those cookies, but it’s THOSE cookies that matter most. Because… - ...it’s the cookies that will go missing from *other* websites that will have the biggest impact. Where the ChromeCookiePocalypse gets real is for things like programmatic advertising, or anything that builds a user’s profile across sites, or requires a view into the full user journey. Accordingly, the 3rd party cookies on your own site might not be nearly as important as the cookies on other places on the web that enrich the profiles of your potential audience.
I think the reason I’m so frustrated by the messaging is because 1, I hate anything that resembles fear-mongering (especially when it includes the selling of tools and services), and 2, I’ve already seen so much time focused on painstaking cookie audits that don’t actually move an org forward. Focusing on the cookies encourages a bottom-up approach: a lot of backwards engineering to figure out the CURRENT state, rather than taking the steps towards 1st party data… steps that you should be taking regardless. Finding a 3rd party Facebook cookie on your site shouldn’t be how you find out your organization uses targeted advertising, nor should it be the reason you update your strategies. I wonder how much the push to scan websites for cookies and create spreadsheets is because that task, tedious as it is, sounds much more do-able than rethinking your overall data strategy?
If you’re afraid something has slipped through the cracks, then yes, do a cookie audit: go to a conversion point like a purchase confirmation page and look at the 3rd party cookies. Before you research each one, just note the vendors involved. Just seeing that a 3rd party cookie exists gives you a heads up that you have tracking on your site from a vendor that relies on 3rd party cookies for some part of their business model. Because if they’ve got a 3rd party cookie on your site, odds are they use that same cookie on other sites. That’s what you need to solve for: how will your business be affected by your vendors not collecting data on other sites? Don’t focus on the cookie, focus on your strategies. What technology do you have that relies on cross-site tracking? How much of your advertising budget is tied to behavioral profiling? Programmatic advertising? Retargeting? Does your own site serve advertisements that use information learned on other sites? Does your site do personalization or recommendations based on user data collected off your site? What 1st party data do you currently have that could be leveraged to fill in gaps? How can you incentivize more users to authenticate on your site so you can use 1st party identifiers more?
Talk to your marketers and advertising partners. Don’t ask about cookies. Ask what advertising platforms they use. Ask about current (or future) strategies that require some sort of profile of the user. Ask about analysis that requires visibility into what the user is doing on other sites (like view-through conversions, if you still think that’s useful, though you probably shouldn’t). Ask about analysis that relies heavily on attribution beyond a week (which is currently not very reliable and likely to become even less so.)
And, most importantly, talk to the vendors, because it’s going to be up to them to figure out how their business model will work without 3rd party cookies. Most of them will tell you what we already know, but may not be ready to make the most of: 1st party data is the key (which usually means supplementing your client-side online data with data from a CDP or other offline databases). Ask what options there are to supplement client-side tracking with 1st party data (like Meta’s Conversions API). Ask how they might integrate with a Customer Data Platform like Adobe Experience Platform’s Real-Time CDP.
I’m not arguing that we don’t need to make some big changes. In fact, I’m happy the ChromeCookiePocalypse pushed people into thinking more about all of this, even if it was a bit misguided. Technology is changing quickly. Consent is confusing and complicated. Analysts and marketers are having to quickly evolve into data scientists. It’s a lot to keep up with. But words are important, and it’s not just about cookies anymore. Welcome to the “consented-first-party-data future”*.

*I’m open to suggestions for other “cookieless” alternatives